WHY US?
Our Threat Intel should be the first and last line of defense for any network seeking resilience against modern threats.
FAST
You will receive an eradication plan with complete site-wide hacker tools and behaviour analysis within 1 day of our scanner runs. This is facilitated by the seamless collaboration between our expert analysts, our virtual forensic analyst AI and attacker-behaviour modelling technology.

ACCURATE
We provide automated forensic analysis across multiple levels of context that includes the intricate relationships between each of those levels of context.

SIMPLE
Our Incident Response services team walks you through fully-actionable eradication plans, explaining each step simply and clearly.
THOROUGH
We rescan and confirm eradication with cyber threat intel from multiple major proprietary sources, organizations across the globe and through our rigorous AI-driven vetting process.
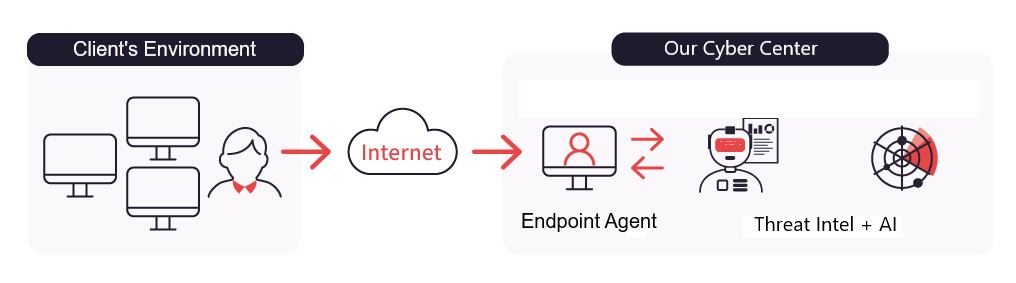
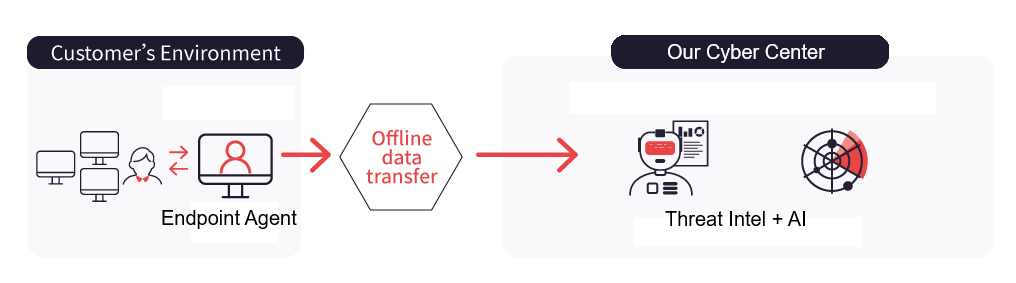
Step 1

Deploy our incident response and forensic scanner to your endpoints.
Step 2
We receive the scanner data & our AI & experts analyze it.
Step 3
We generate a plan & execute it with you.
Step 4

We generate a plan & execute it with you.
We provide you with clear, concise and fully actionable reports covering everything you need to know to get back to healthy status.
 Full storylines of any & all malicious activity
Full storylines of any & all malicious activity
 Malicious domain, IP and URL analysis
Malicious domain, IP and URL analysis
 Malware analysis
Malware analysis
 A step-by-step plan for eradication
A step-by-step plan for eradication
 MITRE ATT&CK mapping
MITRE ATT&CK mapping
 True system-wide root cause analysis
True system-wide root cause analysis
 Graphs of all affected nodes and executions
Graphs of all affected nodes and executions
 Eradication confirmation
Eradication confirmation
 Up-to-date Global Cyber Threat Intelligence
Up-to-date Global Cyber Threat Intelligence